WikiLeaks exposes CIA’s global covert hacking program
The latest WikiLeaks' bombshell of CIA hacking practices, known as Vault 7 has been a wake-up call for computer users and IT giants.
Published: March 9, 2017, 5:17 pm
The international non-profit organisation has unveiled how the CIA has been busy hacking the entire world with spy tools allowing it to infect a target computer bypassing PSPs (Personal Security Product).
The leaked files show how the US spy agency exploited vulnerabilities in well-known software and hardware platforms in order to take control over them, but also revealed details of the CIA’s ability to hide its own hacking fingerprint and attribute it to others.
One of the files, entitled “Kaspersky ‘heapgrd’ DLL Inject,” describes such vulnerabilities of the Russian cybersecurity provider Kaspersky Lab.
“The Kaspersky AVP.EXE process references a DLL called WHEAPGRD.DLL. This DLL is supposed to be located in one of the Kaspersky directories (which are protected by the PSP). Due to a UNICODE/ASCII processing mistake, the DLL name is prepended with the Windows installation drive letter, rather than the full path to the DLL. For typical installations, this causes Kaspersky to look for the DLL ‘CWHEAPGRD.DLL’ by following the standard DLL search path order. Loading our own DLL into the AVP process enables us to bypass Kaspersky’s protections,” the document reads, adding that “this vulnerability is limited to some of Kaspersky’s previous releases.”
Another document reveals a screenshot of a “selected number of DLL misses from Kaspersky TDSS Killer Portable”.
A Kaspersky Lab spokesperson the media the problem had been fixed in 2009 and that all new company products are subject to mandatory testing before release.
Earlier Kaspersky Lab issued an official statement saying it was currently studying the latest leaks. “Kaspersky Lab is thoroughly studying the report published on WikiLeaks on March 7, 2017 in order to make sure that our clients are out of danger. The company pays special attention to such reports and statements.”
Apple and Google rushed to dispel the mounting doubts about their products. “As we’ve reviewed the documents, we’re confident that security updates and protections in both Chrome and Android already shield users from many of these alleged vulnerabilities. Our analysis is ongoing and we will implement any further necessary protections. We’ve always made security a top priority and we continue to invest in our defenses,” Google’s Director of Information Security and Privacy told Recode.net.
The leaks span the period between 2013 and 2016 and presents just the tip of the iceberg. “The CIA found itself building not just its now infamous drone fleet, but a very different type of covert, globe-spanning force — its own substantial fleet of hackers,” the WikiLeaks press release noted.
“In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of public oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons,” WikiLeaks said.
In a move that will likely spark further outrage, BuzzFeed reported that Nigel Farage visited the Wikileaks founder hiding in the Ecuadorian embassy in west London on Thursday. Julian Assange has been living there since he was granted asylum in 2012.
Ecuador’s decision prevented Assange from being deported to Sweden to be questioned over sexual assault allegations and eventually turned over to the USA. The Wikileaks founder has been stranded there ever since, with British police keeping the building under 24/7 close surveillance.
The former UKIP leader spent around 40 minutes in the building and left around midday accompanied by an aide. When questioned by BuzzFeed News, Farage said he couldn’t remember what he was doing in the building. Asked specifically if he had gone to the Knightsbridge building to meet with Assange, Farage said: “I never discuss where I go or who I see”.
The allegations of “digital fingerprints” left behind by Russian hackers at any rate must now be dismissed as either fake or completely meaningless.
The CIA’s Remote Devices Branch’s UMBRAGE group collects and maintains a substantial library of attack techniques “borrowed” from malware produced in other states including the Russian Federation.
With UMBRAGE and related projects the CIA cannot only increase its total number of attack types but also misdirect attribution by leaving behind the “fingerprints” of the groups that the attack techniques were “borrowed” from.
UMBRAGE components not only covers anti-virus (PSP) avoidance and survey techniques, but also keyloggers, password collection, webcam capture, data destruction, persistence, privilege escalation and stealth.
One other document discusses hacking vehicle systems, appearing to indicate the CIA’s interest in hacking recent-model cars with sophisticated onboard computer systems.
In a Facebook livestream, Assange confirmed that the information was obtained from an isolated computer at the CIA headquarters in Virginia. He described the loss as an “historic act of devastating incompetence” for the spy agency.
He also suggested that former US President Barack Obama and current president Donald Trump might not even have known about it. He also questioned if the loss had been shared with companies such as Apple and Google, which were both made vulnerable by it.
“WikiLeaks has a lot more information,” Assange said. “Once this material is effectively disarmed we will publish additional details about what has been occurring,” he added.
WikiLeaks said 7 818 web pages and 943 attachments were published, but were just the first part of more material to come containing details of hacking tools used by the CIA. The organisation has also suggested that some of the data redacted from the initial release, such as all of the actual computer code, might be released in the near future.
Ahead of the press conference today, the organisation asked people to tweet their questions about the leaks using the hashtag #AskWLwikileaks.
The Chinese Foreign Ministry urged the US to stop “stop listening in, monitoring, stealing secrets and internet hacking”.
The German government is examining the leaked data as well. In a statement, the German Foreign Ministry said that it was attempting to authenticate the documents.
“We will initiate an investigation if we see evidence of concrete criminal acts or specific perpetrators,” said the German consulate’s office in the US. “We’re looking at it very carefully.”
All rights reserved. You have permission to quote freely from the articles provided that the source (www.freewestmedia.com) is given. Photos may not be used without our consent.
Consider donating to support our work
Help us to produce more articles like this. FreeWestMedia is depending on donations from our readers to keep going. With your help, we expose the mainstream fake news agenda.
Keep your language polite. Readers from many different countries visit and contribute to Free West Media and we must therefore obey the rules in, for example, Germany. Illegal content will be deleted.
If you have been approved to post comments without preview from FWM, you are responsible for violations of any law. This means that FWM may be forced to cooperate with authorities in a possible crime investigation.
If your comments are subject to preview by FWM, please be patient. We continually review comments but depending on the time of day it can take up to several hours before your comment is reviewed.
We reserve the right to delete comments that are offensive, contain slander or foul language, or are irrelevant to the discussion.

Ohio disaster: When hedge funds manage rail traffic
East PalestineAfter the derailment of a freight train loaded with highly toxic chemicals in the US state of Ohio, a devastating environmental catastrophe may now be imminent. The wagons burned for days, and a "controlled" explosion by the authorities released dangerous gases into the environment.

US President Biden orders ‘spy’ balloon to be shot down
WashingtonThe US President gave the order to shoot down China's "spy balloon". The balloon had caused US Secretary of State Blinken to cancel a trip to Beijing. In the meantime, a second balloon was sighted.

US is heading for a financial ‘catastrophe’ US Treasury Secretary warns
WashingtonOn January 19, 2023, the United States hit its debt ceiling of $31.4 trillion. The country faces a recession if it defaults on its debt, the US Treasury Secretary warned in an interview. Her warning underscored the danger of printing money.

Gun violence: More risk in Chicago and Philadelphia than Iraq, Afghanistan
Providence, Rhode IslandA striking statistic: young Americans are several times more likely to be injured by a gun in cities like Chicago and Philadelphia than they are while serving as a soldier in a foreign country.
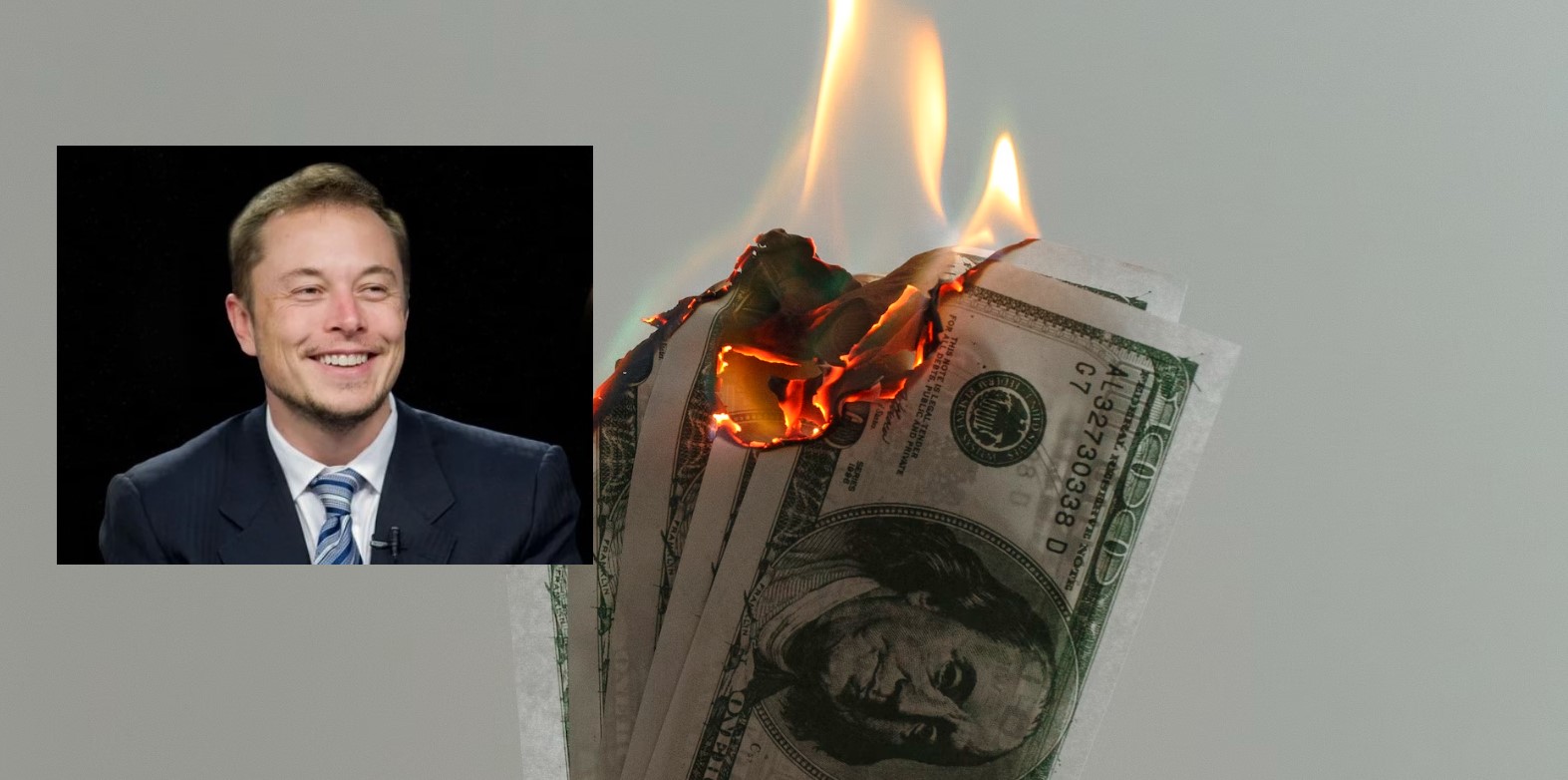
Elon Musk, the first person in history to destroy $200 billion in a year
Never before in human history has a person lost as much money in one year as Elon Musk did in 2022. The Tesla and Twitter boss lost $200 billion last year. However, with his remaining $137 billion, he is still the second richest person in the world.

Extreme cold and winter storms sweep across US
More than a million households without electricity, thousands of canceled flights, temperatures in the double-digit minus range and already 41 fatalities: The US is being overwhelmed by an enormous cold wave.

Soros sponsors violent leftists and anti-police lobby as US crime surges
WashingtonThe mega-speculator and "philanthropist" George Soros remains true to himself – he has been sponsoring anti-police left-wing groups with billions of dollars.

FTX Founder Sam Bankman-Fried arrested after crypto billions go missing
NassauHe is no longer sitting in his fancy penthouse, but in a cell in the Bahamas: Sam Bankman-Fried (30), founder of the crypto company FTX, is said to be responsible for the theft of 37 billion euros. An interesting fact is that media in the EU have so far kept this crime thriller almost completely secret.
How Twitter helped Biden win the US presidency
WashingtonThe short message service Twitter massively influenced the US presidential election campaign two years ago in favor of the then candidate Joe Biden. The then incumbent Donald Trump ultimately lost the election. Internal e-mails that the new owner, Elon Musk, has now published on the short message service show how censorship worked on Twitter. The 51-year-old called it the “Twitter files”.

Alberta PM suspends cooperation with WEF
EdmontonThe newly elected Premier Danielle Smith of the province of Alberta in Canada has recently made several powerful statements against the globalist foundation World Economic Forum and its leader Klaus Schwab. She has also decided to cancel a strange consulting agreement that WEF had with the state.






