Another huge cyber attack is underway
Another huge cyberattack is underway after last week's assault on computers worldwide, according to a global cybersecurity firm, suggesting military-grade cyberweapons are now being deployed for cyber crime.
Published: May 18, 2017, 11:21 am
Cyber bandits used EternalBlue and DoublePulsar, developed by the NSA and released by the ShadowBrokers hackers back in April. The attackers used both these exploits to install the cryptocurrency miner Adylkuzz.
“We don’t know how big it is” but “it’s much bigger than WannaCry”, Proofpoint’s vice president for email products, Robert Holmes, told AFP on Wednesday.
The WannaCry cyberattack paralyzed computer systems worldwide. In Freiburg, Germany, a passenger told FWM, that all electronic noticeboards were down and transport interrupted. Not only Deutsche Bahn rail network were among those hit, but also Britain’s National Health Service, US package delivery giant FedEx and Spanish telecoms giant Telefonica.
US officials on Tuesday put the number of computers infected by WannaCry at over 300 000. Despite a quick breakthrough that caused WannaCry to be slowed down, researchers don’t yet fully understand it.
“The problem is that we’re still not certain about the origin of the infections” because it wasn’t via emails which deceive users into installing the virus, an expert told AFP on condition of anonymity.
The latest attack targets the same vulnerabilities as the WannaCry ransomware, but uses the hundreds of thousands of computers believed to have been infected to mine virtual currency.
Researchers at Proofpoint have discovered Adylkuzz, said Nicolas Godier, a researcher at the computer security firm. “It uses the hacking tools recently disclosed by the NSA and which have since been fixed by Microsoft in a more stealthy manner and for a different purpose,” he said.
Virtual currencies such as Monero and Bitcoin make use of volunteers computers to record transactions.
According to Proofpoint the attack include loss of access to shared Windows resources and degradation of PC and server performance. “As it is silent and doesn’t trouble the user, the Adylkuzz attack is much more profitable for the cyber criminals. It transforms the infected users into unwitting financial supporters of their attackers,” said Godier.
Adylkuzz may have been infecting computers since at least May 2, and perhaps even since April 24, but due to its stealthy nature was not immediately detected.
Shadow Broker hackers also released a data dump allegedly stolen from the NSA that details the agency’s ability to hack international banks, as well as the SWIFT network, via Windows PCs and servers used in global financial transfers.
Dubbed ‘Lost in Translation,’ the hack lists Qatar First Investment Bank, Dubai Gold and Commodities Exchange and Tadhamon International Islamic Bank as allegedly compromised.
One of the world’s most secure methods of making payment orders has been compromised as the hacking tools are now freely available online.
Adylkuzz initially prevents cybersecurity professionals from identifying that there is a problem.
While the term cryptocurrency is typically associated with Bitcoin, Adylkuzz actually mines Monero, a similar but more heavily encrypted digital currency. Monero became popular after it was adopted in the AlphaBay market on the Dark Web. One monero is roughly equivalent to $27 at current exchange rates.
The attackers regularly changes the online payment address to avoid attracting attention.
As in the case of the WannaCry attack, hackers used the NSA’s weaponized tools of Microsoft operating systems to infect hundreds of thousands of machines worldwide with malware, and many more are expected in the future.
All rights reserved. You have permission to quote freely from the articles provided that the source (www.freewestmedia.com) is given. Photos may not be used without our consent.
Consider donating to support our work
Help us to produce more articles like this. FreeWestMedia is depending on donations from our readers to keep going. With your help, we expose the mainstream fake news agenda.
Keep your language polite. Readers from many different countries visit and contribute to Free West Media and we must therefore obey the rules in, for example, Germany. Illegal content will be deleted.
If you have been approved to post comments without preview from FWM, you are responsible for violations of any law. This means that FWM may be forced to cooperate with authorities in a possible crime investigation.
If your comments are subject to preview by FWM, please be patient. We continually review comments but depending on the time of day it can take up to several hours before your comment is reviewed.
We reserve the right to delete comments that are offensive, contain slander or foul language, or are irrelevant to the discussion.

Ohio disaster: When hedge funds manage rail traffic
East PalestineAfter the derailment of a freight train loaded with highly toxic chemicals in the US state of Ohio, a devastating environmental catastrophe may now be imminent. The wagons burned for days, and a "controlled" explosion by the authorities released dangerous gases into the environment.

US President Biden orders ‘spy’ balloon to be shot down
WashingtonThe US President gave the order to shoot down China's "spy balloon". The balloon had caused US Secretary of State Blinken to cancel a trip to Beijing. In the meantime, a second balloon was sighted.

US is heading for a financial ‘catastrophe’ US Treasury Secretary warns
WashingtonOn January 19, 2023, the United States hit its debt ceiling of $31.4 trillion. The country faces a recession if it defaults on its debt, the US Treasury Secretary warned in an interview. Her warning underscored the danger of printing money.

Gun violence: More risk in Chicago and Philadelphia than Iraq, Afghanistan
Providence, Rhode IslandA striking statistic: young Americans are several times more likely to be injured by a gun in cities like Chicago and Philadelphia than they are while serving as a soldier in a foreign country.
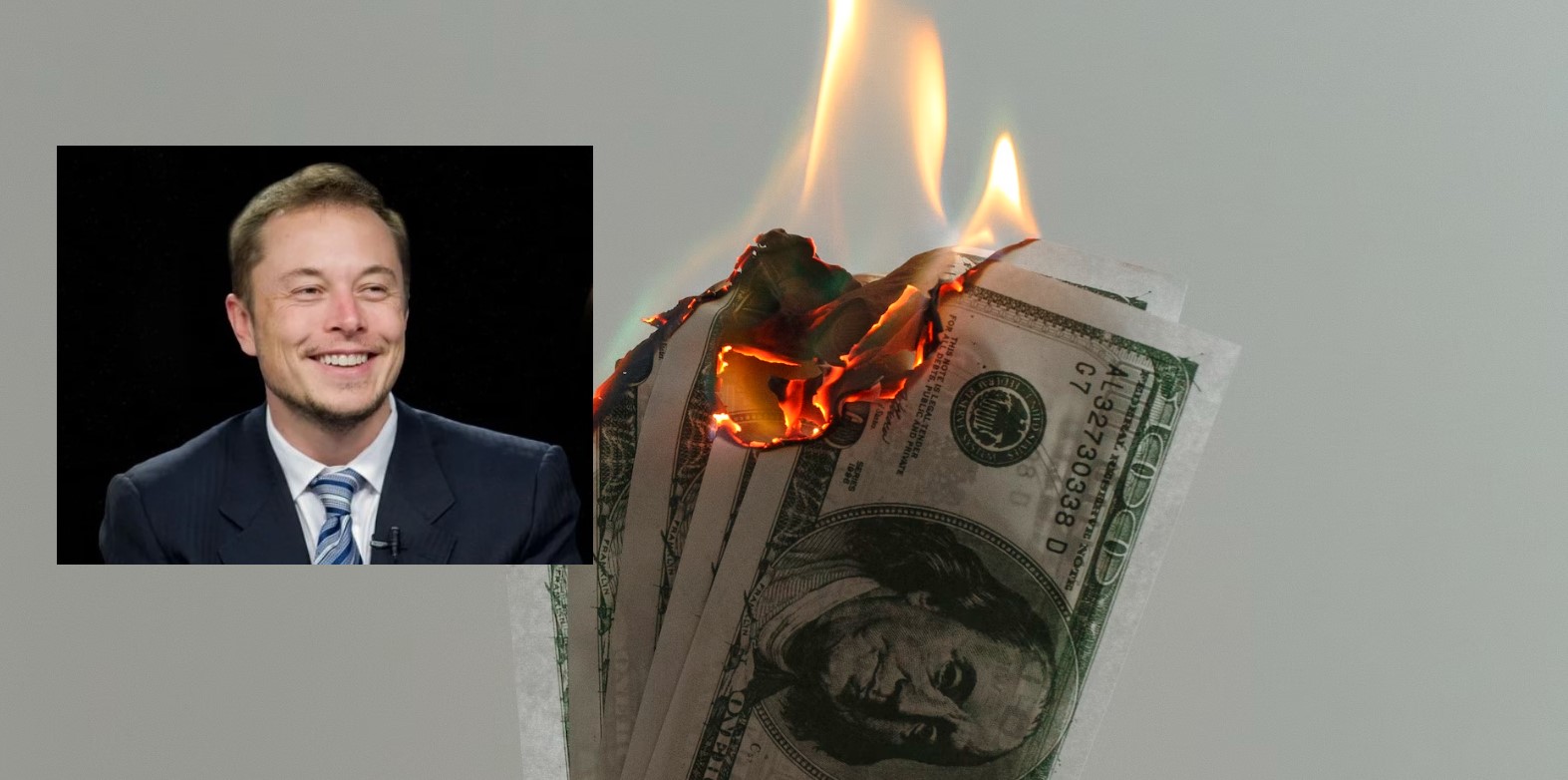
Elon Musk, the first person in history to destroy $200 billion in a year
Never before in human history has a person lost as much money in one year as Elon Musk did in 2022. The Tesla and Twitter boss lost $200 billion last year. However, with his remaining $137 billion, he is still the second richest person in the world.

Extreme cold and winter storms sweep across US
More than a million households without electricity, thousands of canceled flights, temperatures in the double-digit minus range and already 41 fatalities: The US is being overwhelmed by an enormous cold wave.

Soros sponsors violent leftists and anti-police lobby as US crime surges
WashingtonThe mega-speculator and "philanthropist" George Soros remains true to himself – he has been sponsoring anti-police left-wing groups with billions of dollars.

FTX Founder Sam Bankman-Fried arrested after crypto billions go missing
NassauHe is no longer sitting in his fancy penthouse, but in a cell in the Bahamas: Sam Bankman-Fried (30), founder of the crypto company FTX, is said to be responsible for the theft of 37 billion euros. An interesting fact is that media in the EU have so far kept this crime thriller almost completely secret.
How Twitter helped Biden win the US presidency
WashingtonThe short message service Twitter massively influenced the US presidential election campaign two years ago in favor of the then candidate Joe Biden. The then incumbent Donald Trump ultimately lost the election. Internal e-mails that the new owner, Elon Musk, has now published on the short message service show how censorship worked on Twitter. The 51-year-old called it the “Twitter files”.

Alberta PM suspends cooperation with WEF
EdmontonThe newly elected Premier Danielle Smith of the province of Alberta in Canada has recently made several powerful statements against the globalist foundation World Economic Forum and its leader Klaus Schwab. She has also decided to cancel a strange consulting agreement that WEF had with the state.






