The ‘Internet apocalypse’ that nobody cares about
A historic event of unprecedented magnitude that will keep the specialists busy for many months to come: This information has not exited the mainstream media nor the public at large.
Published: January 29, 2022, 11:55 am
“Log4j” is not known to anyone outside of developer circles. And many who use this piece of computer code are not even aware of its vulnerability. For PCs, smartphones, game consoles and internet-enabled objects in general, it is one of the most used programs in the world with up to a billion downloads per year. Because of its severity, the Log4j vulnerability has been given its own name. It’s called “Log4Shell”.
Some 25 years ago, Ceki Gülcü, who now owns his own software consulting company, wrote his master’s thesis in cryptography at the IBM research laboratory near Zurich in Switzerland. After his studies, he remained employed in an IBM team that dealt with data security.
The software he developed writes down what happens when you use software and Log4j version 1 was created. Ceki Gülcü explained the functionality of Log4j using the example of the black box in an airplane, which records the conversations of the pilots, the speed, the altitude and all the technical aspects that are programmed to monitor and control the flight.
Log4j’s software is open source, i.e. software that is made available to the general public free of charge. Such software has a reputation for being generally safe precisely because of its transparency. It is assumed that many eyes ensure that possible problems are recognized and solved.
In 2000, the program was officially handed over to the Apache open source foundation. This non-profit foundation is made up of volunteer developers and contributors. In 2006, Ceki Gülcü left the project and developed his own software such as SLF4J or LogBack, which are well known and popular today.
In 2012, the Apache Foundation started a complete revision under the name Log4j Version 2. A special function was introduced: Log4j 2 analyzes and interprets external programs before their content is used further.
And this is exactly where the vulnerability was discovered over a month ago: An attacker can submit a specially crafted file that Log4j falsely accepts. This means that any code from external sources can be executed. Another option is to simply freeze the compromised computer and then demand a ransom.
The discovery of the vulnerability reads like a thriller. It was Chen Zhaojun, a member of the Alibaba Cloud Security team, who discovered the vulnerability. He informed the Apache Foundation and together with them made the vulnerability public on December 9, 2021, giving the developers enough time to fix the problem. After a leak on a Chinese blogging platform shortly before publication, there were discussions about the details of the vulnerability. Hackers didn’t wait: the first attacks were observed in the first few days after discovery.
Maximum damage
Giants like NASA, Twitter, Oracle and Apple are known to use programs in which the Log4j vulnerability is present. For example, iCloud, Apple’s online storage service, could have been hacked via this vulnerability. In theory, the small helicopter that NASA sent to Mars is also vulnerable, as some of the programs used to communicate with it from Earth are based on Log4j. Small and medium-sized businesses, government agencies and even individuals with private servers at home are also affected, and it will take some time before the extent of the gap is known.
Furthermore, it is clear that the Belgian Ministry of Defense was the first known victim of a Log4Shell attack. Spectacular precautionary measures were taken, for example in Canada with the preventive shutdown of government servers or in Germany with the giant company Bosch, which also manufactures connected objects and admitted to being affected, but without giving further details.
Actually, this vulnerability may have been discovered and exploited by hackers long before, without anyone noticing. As a reminder, version 2 was released in 2012. It is therefore not impossible that criminals could have smuggled malicious programs into computer systems. For some actors, gaining access to confidential information is more attractive than being paid for it. It is feared that the first wave of attacks was just an initial earthquake before a tsunami of larger attacks.
What should a digital future look like?
The fact is that neither society nor governments are prepared for accelerated digitization today.
Before governments continue to push for electronic voting and the automated exchange of medical data, societies should discuss the kind of future they want. This includes a public discussion on the legal aspects, security and data protection, infrastructure, open source, surveillance, sovereignty over our data, democracy, culture, copyright. And of course censorship must also be included in the discussions. And public participation is necessary because the transition concerns us all – we urgently need to assume digital responsibility.
This “computer apocalypse” raises the question of the importance of our digital world. Contingency plans should be put in place since technical measures alone are not enough. Countries and businesses need to prepare to continue working in the event of a larger network failure. In addition, crisis communication infrastructure should be planned.
Each person is responsible for the security of their own computer system and makes sure to know the basics of home privacy: All sensitive data should be kept in a separate area from the internet. Change the passwords regularly, as well as the password for a WLAN and install a password on any hard drive.
All rights reserved. You have permission to quote freely from the articles provided that the source (www.freewestmedia.com) is given. Photos may not be used without our consent.
Consider donating to support our work
Help us to produce more articles like this. FreeWestMedia is depending on donations from our readers to keep going. With your help, we expose the mainstream fake news agenda.
Keep your language polite. Readers from many different countries visit and contribute to Free West Media and we must therefore obey the rules in, for example, Germany. Illegal content will be deleted.
If you have been approved to post comments without preview from FWM, you are responsible for violations of any law. This means that FWM may be forced to cooperate with authorities in a possible crime investigation.
If your comments are subject to preview by FWM, please be patient. We continually review comments but depending on the time of day it can take up to several hours before your comment is reviewed.
We reserve the right to delete comments that are offensive, contain slander or foul language, or are irrelevant to the discussion.

NOAA Predicts Zero Sunspots for Almost the Whole 2030s
CLIMATEThe United States' government scientific organization, the National Oceanic and Atmospheric Administration (NOAA), predicts zero sunspots from 2031 to 2040. This is an extreme situation that has not occurred in as long as humanity has been counting sunspots, and it leads us into uncharted territory in terms of our solar system. However, this prediction aligns with the warnings of the world-renowned solar researcher Valentina Zharkova for many years, who indicated in 2019 various signs of this catastrophic phenomenon, including the extreme hailstorms we have seen in Europe and the world this summer. The forecast and various observations this year give cause for very significant concern. In this unique analysis, Free West Media explains why.

European Nationalist Parties Forge Cooperation Ahead of EU Elections
EUROPEAN ELECTIONSOn Saturday, August 26, representatives of six European nationalist parties gathered in Budapest. The meeting was initiated by the Hungarian party Mi Hazánk and took place in the national parliament. Representatives of the parties signed a joint declaration that not only reaffirms the parties' friendship but also their unity on a range of complex political issues. A surprisingly clear and radical manifesto was established. The hope is that this cooperation will lead to success in the EU elections and eventually result in the formation of a group in the European Parliament. For Swedish nationalism, this meeting marks a success as Sweden, for the first time, has a party represented in a leading nationalist cooperation in Europe. Free West Media was present at this historic event.

Turkey Believes Sweden Hasn’t Done Enough
Sweden will have to wait a bit longer for NATO membership, according to Turkey's Justice Minister Jilmaz Tunc. First, Sweden must extradite the "terrorists" Turkey wants and stop the desecration of the Quran.

Swedish Weapon Takes Down Russia’s Best Attack Helicopter
The Russian attack helicopter Ka-52 is considered one of the world's best and has struck fear in Ukraine, where it has hunted down tanks and other armored vehicles, often beyond the range of many light anti-aircraft systems. However, it has met its match in the Swedish air defense missile system RBS 70, which has quickly led to significant losses for the Russian helicopter forces.

Strong Confidence in German AfD
Alternative for Germany (AfD) held a party conference on July 29-30 to select candidates for the upcoming EU election next year. EU Parliament member Maximilian Krah, belonging to the party's more radical, ethnonationalist faction, was appointed as the top candidate. The party's two spokespersons delivered powerful speeches criticizing the EU's failed migration policy and trade sanctions that isolate Europe and Germany from the rest of the world. They argued that it's time for the EU to return a significant portion of its power to national parliaments. However, they have dropped the demand for Germany to exit the EU.

The Establishment Wants to Ban Germany’s Second Largest Party – for the Sake of Democracy
The rising popularity of AfD has raised strong concerns within the establishment. Despite lies and demonization in the media and isolation from the overall political establishment, the party continues to grow. Certain representatives of the party are accused of becoming increasingly "extreme," and in an unusual move, the influential weekly newspaper Der Spiegel demanded that AfD be "banned."

Dutch FvD break through the media blockade
What is happening in the Netherlands? It is often difficult to follow events in other countries, especially when distorted by system media. We give Forum for Democracy (FvD) the opportunity to speak out on the political situation in the Netherlands and the staunch resistance they face in trying to save the country.
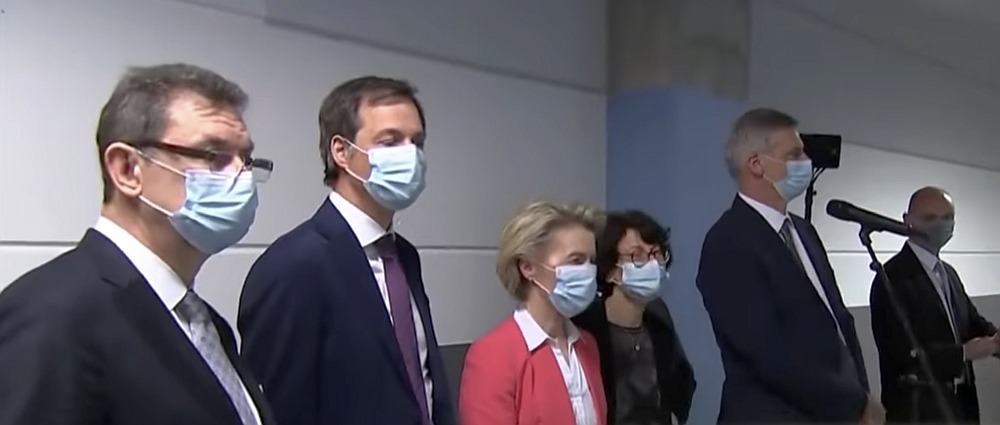
The Ursula von der Leyen Affair
After a criminal complaint in Belgium against the President of the European Commission, the so-called SMS-case, now takes a new turn. The judge responsible for the investigation will likely gain access to the secret messages exchanged between Ursula von der Leyen and Albert Bourla, CEO of Pfizer, at least if they haven't been deleted.

Publisher of Unique Literature Worldwide Blocked by International Distributor
Arktos has distinguished itself by publishing groundbreaking philosophers and social critics. Now, the publisher's international distributor has abruptly terminated the cooperation, and more than 400 already printed titles cannot reach their audience. There is strong evidence that the distributor has been under pressure, something that has also happened in Sweden. We have spoken with Arktos founder Daniel Friberg about the ongoing struggle for freedom of speech in a shrinking cultural corridor.
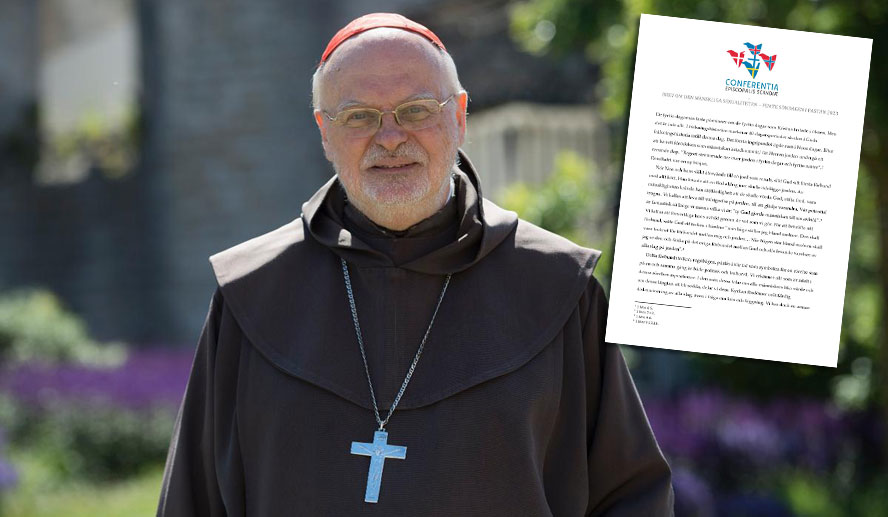
Care prompts bishops to criticize transgender ideology
The Catholic bishops of the Scandinavian countries presented an open five-page letter criticizing transgender ideology on March 21, just before Easter. The document primarily expresses care and advice and was read aloud in Catholic churches in Sweden, Norway, Finland, Denmark, and Iceland. Cardinal Anders Arborelius, Bishop of Stockholm, is one of the signatories of the document.






