Britain does not exclude preventive nuclear attack in latest cyber defence review
A "kinetic" response, across the board, even nuclear, underpins the new British national strategy that will shape the operational guidelines for the UK, post-Brexit. It does not exclude any scenario should the country be hit by a hostile attack from a foreign power and is aimed at partially or totally “blinding” the protection capabilities of infrastructures or systems that are critical for the safety of the population and economic activity.
Published: April 6, 2021, 10:51 am
The government of Boris Johnson, in line with the new priorities that the US and structures such as NATO have highlighted, considers cyber competition to be central as a determinant of the strategic equilibrium of the coming decades and in the document “Global Britain in a competitive age” it mentions the cyber issue 148 times, always in relation to the need to assume a more accentuated operational posture towards a dual approach, which integrates the military and civil spheres in the defence of the country’s digital assets.
London defines itself as a “responsible power” in the cyber field, and claims to have the third largest operational capability in the world in terms of defence, resilience and coordination of intelligence.
This vision was confirmed in 2019 in the Italian daily Corriere della Sera by the current Italian Minister for Innovation in the Draghi government, Vittorio Colao, according to whom the United Kingdom is at the forefront of Europe and the United States on the evaluation of the risks related to cybersecurity. The strengthening of the National Cyber Force, from this point of view, is considered central to allowing any threats to be disrupted with direct or preventive actions. Thus, London is ready for anything should an attack pierce its cyber security perimeter.
Giuseppe Gagliano, one of the leading Italian scholars of asymmetric wars, highlighted in Notizie Geopolitiche, that London has not ruled out in the most recent defence review, the possibility of a nuclear response to “computer operations that cause or present an imminent threat of death and destruction on scale equivalent to an armed attack” in reference to actions comparable to “a destructive attack against the industrial control systems of one or more of the critical sectors, such as water, energy, health or finance” capable of causing paralysis to the country’s system.
For some time already, cyber issues have been included in the national security perimeters of all the major powers, and the doctrines of cyberwarfare are becoming more kinetic, dynamic and extensive. The main nature of problems linked to cyberwar however, is the blurred boundary between defensive operations and offensive actions since it includes all forms of attack and defence in cyberspace, representing an extension of electronic warfare in its aspects both offensive and defensive (countermeasures, wiretapping, etc.) and defensive (countermeasures, encryption, firewalls or barriers to prevent access to networks and databases) and often closely coordinated with the consequent political aims – strategic and economic.
The United Kingdom has now raised the bar and inserted cyber notions into areas where an offensive is to be considered comparable to a large-scale frontal attack, not excluding maximum retaliation. This declaration certainly has a deterrent value (and in the phase of strengthening the nuclear arsenal it is not surprising) but it also underlines the geostrategic value of cyber warfare.
The cyber domino, for its intrinsic vulnerability, for its pervasiveness, for the impunity it grants, is exposed to threats coming from different directions and potentially destructive asymmetrical moves. Furthermore, in times of a pandemic, the dependence of the main critical infrastructure of the economic and financial fabric on digitized information systems, the expansion of smart offices and the considerable exposure of citizens’ data, has imposed reflection in all the most advanced nations on the most optimal nature of protection. Since the Stuxnet case, the virus launched by the US and Israel against Iran in 2010, all military decision-makers have been focusing on this complicated field of competition.
London has deployed its cyber force to the Five Eyes, the spy block formed by the leading countries of the Anglosphere (United Kingdom, Canada, Australia, New Zealand) and the USA, to defend itself on the cyber front. But it is ready to act autonomously if a rival state attempts an offensive.
The reference to the final weapon, the atomic bomb, clearly signals the importance of the matter. At the same time, it highlights the need for an in-depth reflection on the rules of engagement in the cyber field since there is an obligation to distinguish between sovereign states, criminal groups and hackers operating with false-flag intentions which makes it an extremely complex problem to address.
Needless to say, the big danger is accurate attribution of attacks, with most cyber experts suggesting that it is impossible to be certain about where online attackers are based or who they really work for.
The 2021 British Defence Report states that the nation will not use nuclear weapons against any non-nuclear state that is party to the 1968 Nuclear Non-Proliferation Treaty (NPT). But then it adds that “we reserve the right to review this guarantee if the future threat of weapons of mass destruction, such as chemical and biological capabilities, or emerging technologies that could have a comparable impact, make it necessary”.
In another passage, the report clarifies that “cyber” is considered an “emerging technology”. This evidently means that the UK will consider a nuclear response to a major cyber attack.
In 2018 Air Marshall Phil Collins, Chief of Defence Intelligence, said the UK’s position should be to seek a rapid but controlled exploitation of vulnerabilities and the proactive denial of opportunities. Around the same time, UK Attorney General Jeremy Wright QC MP had stated that the UK believed it was clear that cyber operations would give Britain an intrinsic right to act in self-defence, as recognized in Article 51 of the Charter of the United Nations. These two statements made it clear already that the UK believes it has the right to kinetically respond to cyberattacks, even if the response is preventive.
The new ability of the National Cyber Force (NCF) brings together the personnel of GCHQ and MOD, as well as the Secret Intelligence Service (SIS) and the Defence Science and Technology Laboratory, for the first time under a single unified command.
All rights reserved. You have permission to quote freely from the articles provided that the source (www.freewestmedia.com) is given. Photos may not be used without our consent.
Consider donating to support our work
Help us to produce more articles like this. FreeWestMedia is depending on donations from our readers to keep going. With your help, we expose the mainstream fake news agenda.
Keep your language polite. Readers from many different countries visit and contribute to Free West Media and we must therefore obey the rules in, for example, Germany. Illegal content will be deleted.
If you have been approved to post comments without preview from FWM, you are responsible for violations of any law. This means that FWM may be forced to cooperate with authorities in a possible crime investigation.
If your comments are subject to preview by FWM, please be patient. We continually review comments but depending on the time of day it can take up to several hours before your comment is reviewed.
We reserve the right to delete comments that are offensive, contain slander or foul language, or are irrelevant to the discussion.
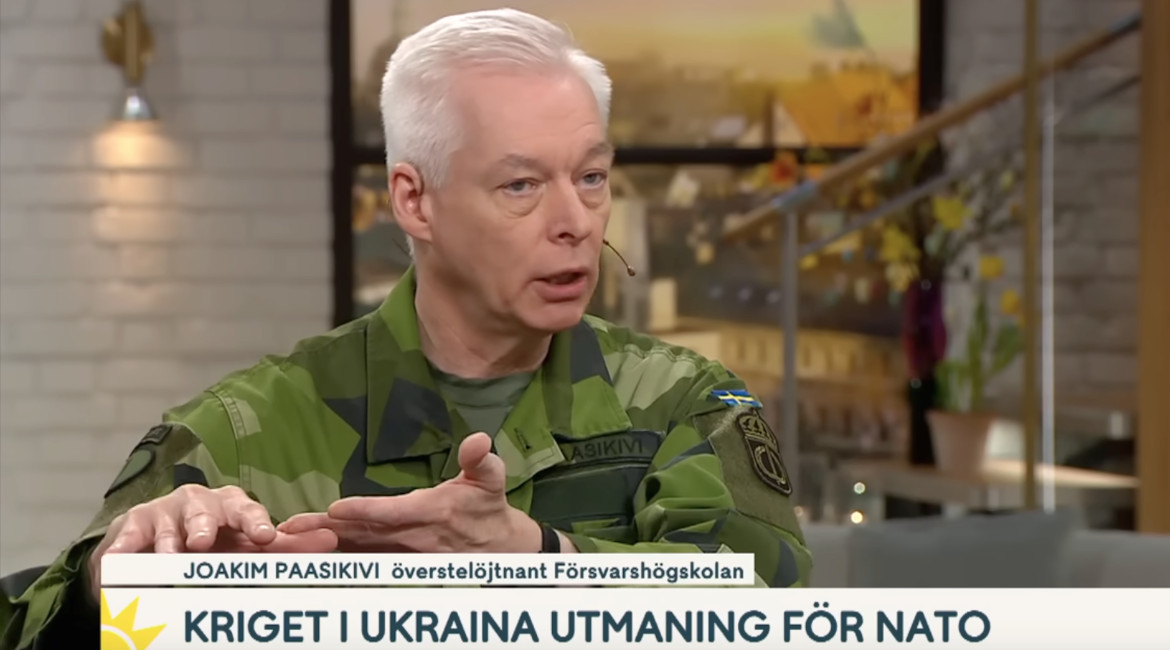
Swedish military wants to remilitarize the Åland Islands
The demilitarized autonomy has previously been known as 'the islands of peace.

NOAA Predicts Zero Sunspots for Almost the Whole 2030s
CLIMATEThe United States' government scientific organization, the National Oceanic and Atmospheric Administration (NOAA), predicts zero sunspots from 2031 to 2040. This is an extreme situation that has not occurred in as long as humanity has been counting sunspots, and it leads us into uncharted territory in terms of our solar system. However, this prediction aligns with the warnings of the world-renowned solar researcher Valentina Zharkova for many years, who indicated in 2019 various signs of this catastrophic phenomenon, including the extreme hailstorms we have seen in Europe and the world this summer. The forecast and various observations this year give cause for very significant concern. In this unique analysis, Free West Media explains why.

European Nationalist Parties Forge Cooperation Ahead of EU Elections
EUROPEAN ELECTIONSOn Saturday, August 26, representatives of six European nationalist parties gathered in Budapest. The meeting was initiated by the Hungarian party Mi Hazánk and took place in the national parliament. Representatives of the parties signed a joint declaration that not only reaffirms the parties' friendship but also their unity on a range of complex political issues. A surprisingly clear and radical manifesto was established. The hope is that this cooperation will lead to success in the EU elections and eventually result in the formation of a group in the European Parliament. For Swedish nationalism, this meeting marks a success as Sweden, for the first time, has a party represented in a leading nationalist cooperation in Europe. Free West Media was present at this historic event.

Turkey Believes Sweden Hasn’t Done Enough
Sweden will have to wait a bit longer for NATO membership, according to Turkey's Justice Minister Jilmaz Tunc. First, Sweden must extradite the "terrorists" Turkey wants and stop the desecration of the Quran.

Swedish Weapon Takes Down Russia’s Best Attack Helicopter
The Russian attack helicopter Ka-52 is considered one of the world's best and has struck fear in Ukraine, where it has hunted down tanks and other armored vehicles, often beyond the range of many light anti-aircraft systems. However, it has met its match in the Swedish air defense missile system RBS 70, which has quickly led to significant losses for the Russian helicopter forces.

Strong Confidence in German AfD
Alternative for Germany (AfD) held a party conference on July 29-30 to select candidates for the upcoming EU election next year. EU Parliament member Maximilian Krah, belonging to the party's more radical, ethnonationalist faction, was appointed as the top candidate. The party's two spokespersons delivered powerful speeches criticizing the EU's failed migration policy and trade sanctions that isolate Europe and Germany from the rest of the world. They argued that it's time for the EU to return a significant portion of its power to national parliaments. However, they have dropped the demand for Germany to exit the EU.

The Establishment Wants to Ban Germany’s Second Largest Party – for the Sake of Democracy
The rising popularity of AfD has raised strong concerns within the establishment. Despite lies and demonization in the media and isolation from the overall political establishment, the party continues to grow. Certain representatives of the party are accused of becoming increasingly "extreme," and in an unusual move, the influential weekly newspaper Der Spiegel demanded that AfD be "banned."

Dutch FvD break through the media blockade
What is happening in the Netherlands? It is often difficult to follow events in other countries, especially when distorted by system media. We give Forum for Democracy (FvD) the opportunity to speak out on the political situation in the Netherlands and the staunch resistance they face in trying to save the country.
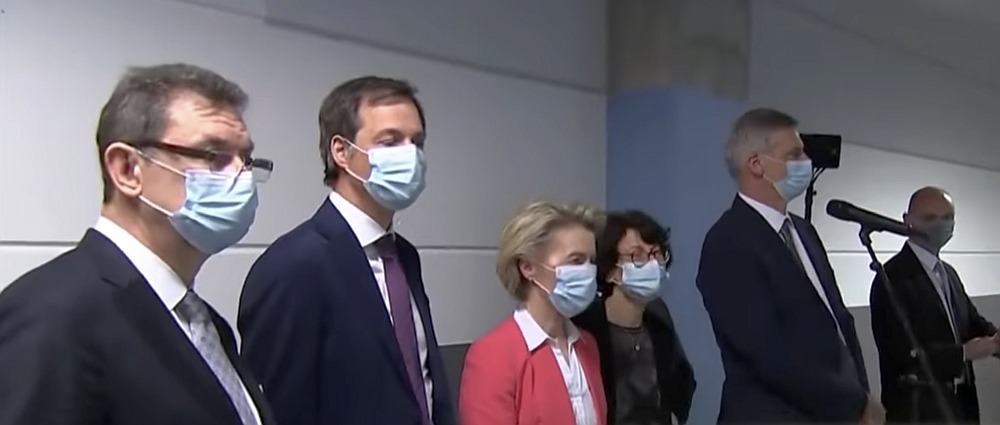
The Ursula von der Leyen Affair
After a criminal complaint in Belgium against the President of the European Commission, the so-called SMS-case, now takes a new turn. The judge responsible for the investigation will likely gain access to the secret messages exchanged between Ursula von der Leyen and Albert Bourla, CEO of Pfizer, at least if they haven't been deleted.

Publisher of Unique Literature Worldwide Blocked by International Distributor
Arktos has distinguished itself by publishing groundbreaking philosophers and social critics. Now, the publisher's international distributor has abruptly terminated the cooperation, and more than 400 already printed titles cannot reach their audience. There is strong evidence that the distributor has been under pressure, something that has also happened in Sweden. We have spoken with Arktos founder Daniel Friberg about the ongoing struggle for freedom of speech in a shrinking cultural corridor.

